DataSunrise Audit for Teradata
Though it may seem that data auditing is only about reporting and statistics, it’s one of the most critical components of any database security system. Auditing helps to reveal and investigate data leaks and data breaches. It is especially important when working with Big data.
Teradata audit tool by DataSunrise keeps record of all user actions and changes made to your Teradata contents. Couple it with SIEM system and you will be always aware of what is going on with your database.
It is hard to imagine an efficient up-to-date security system without database auditing tool, but usually standard auditing tools don’t satisfy all requirements of companies that don’t underestimate the importance of information security. Teradata audit tool by DataSunrise is designed to help you finally make a choice of database monitoring system. Using Data Audit will provide you some valuable advantages:
- No database slowdown, easy to deploy;
- Simple interface with a lot of customizable features that help to automate some aspects of database monitoring and security management;
- Provides real-time visibility into all database activity, including privileged user access, because inside threats are even more dangerous than outside hacker attacks;
- Makes it easier to demonstrate compliance with government and industry standards such as SOX, PCI-DSS, HIPAA and others;
- Has a self-learning system to divide SQL queries into queries typical for given database environment and unusual queries, which saves time and simplifies inspecting process;
- There is an opportunity to notify about any suspicious activity, it minimizes risks by stopping attacks before they cause damage.
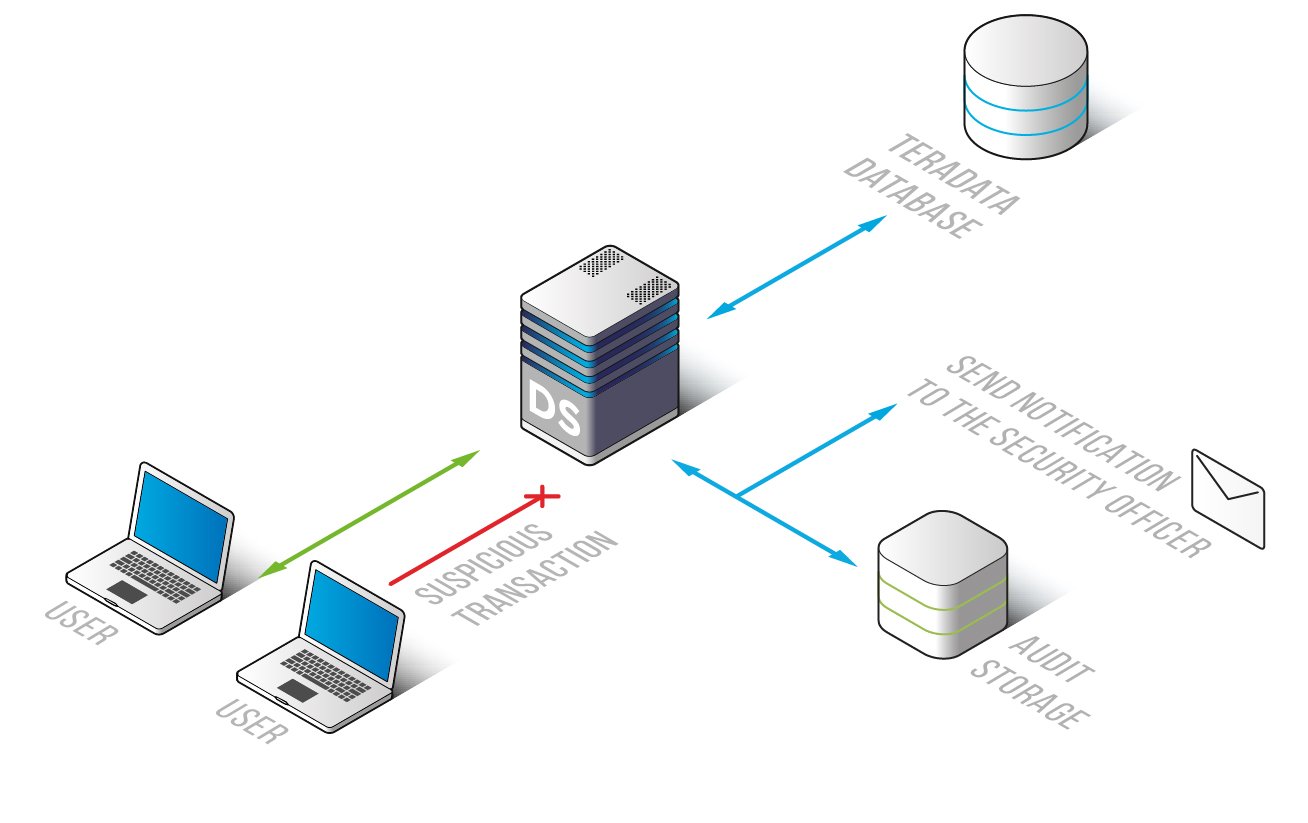
Teradata audit tool by DataSunrise allows monitoring and logging of access to a database with regulated detailed information of all database transactions from login to logoff. More detailed information on monitoring feature is available here. Audit results are saved into an external database or exported to any SIEM system.
Teradata audit tool by DataSunrise is a helpful tool to detect SQL injections, brute-force logins, abnormal access patterns and other indicators that your database might have been breached, it is also valuable in retaining the information about data leaks and data breaches. Curious about DataSunrise Audit? Let’s meet online for a tailored demo of our advanced data management capabilities. Choose your preferred time slot!


