DataSunrise Audit for MySQL
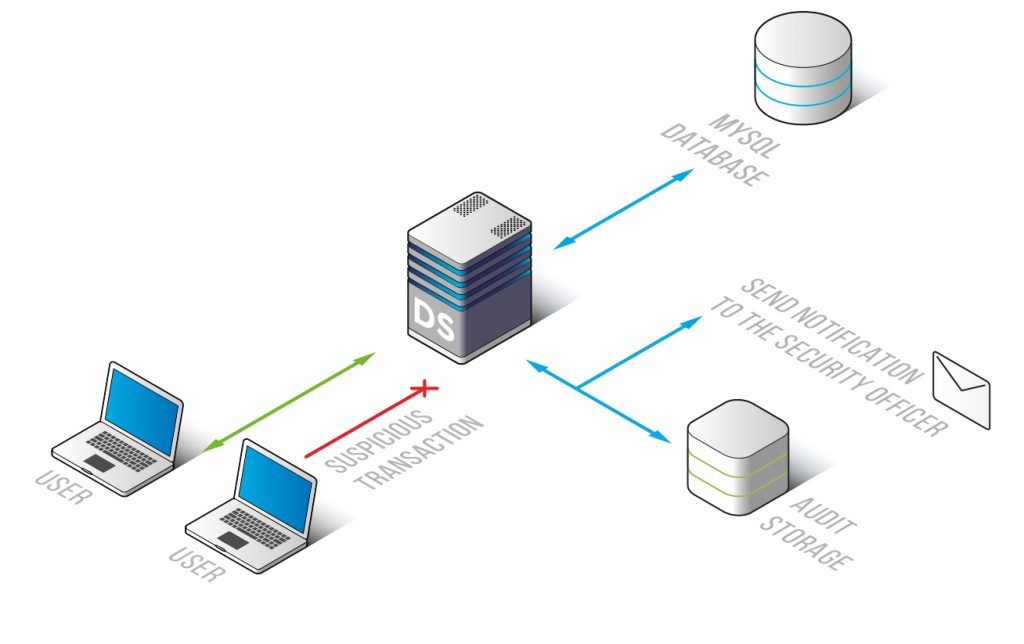
DataSunrise’s real-time MySQL audit tool monitors incoming traffic. It uses a White List of safe SQL queries set by an administrator. This ensures that we only allow approved queries.
Database activity tracking ability blocks any attacks on MySQL, prevents unauthorized access and guarantees effective data protection. Nonstop monitoring is a part of any investigation process as well.
DataSunrise Data Audit for MySQL database enables real-time tracking of changes with data, database structure and user actions. Audit records have information about database operations. The sentence shows who did the operation, when they did it, and all the operation details.
Organizations must follow security rules and use data audit tools to track all actions involving personal information. The system stores audit logs in an internal or external database for further examination or forensic purposes. A feature exists to generate specialized reports for specific types of transactions.
Databases can track changes, but some DBAs don’t use them because they worry it will slow things down and cause errors. The built-in audit features can slow down the database’s performance and lead to data problems.
DataSunrise Data Audit can monitor database activity without affecting database or applications, avoiding performance or scalability issues. DataSunrise data audit solution helps DBAs prevent security threats. It watches database transactions and alerts about any unusual activity not on the approved list.
DataSunrise supports Syslog – the most widely used protocol for message logging. This enables to integrate the firewall with Security Information and Event Management (SIEM) solutions and enhance security analytics capabilities of a used SIEM solution. Integrated with SIEM system Datasunrise helps to achieve full visibility of database transactions and user activity. More detailed information on monitoring feature is available here.
DataSunrise Data Audit retrieves and logs the following data:
- Codes of SQL queries and the results of their execution ;
- Session details;
- Number of rows affected by a query, database errors;
- Data on client applications used to query the database.
DataSunrise’s MySQL audit solution can save audit results in SQLite, PostgreSQL, Amazon Aurora, Amazon Redshift, or MySQL databases. It can also export event logs to an external SIEM system.


