DataSunrise Audit for Google Cloud SQL
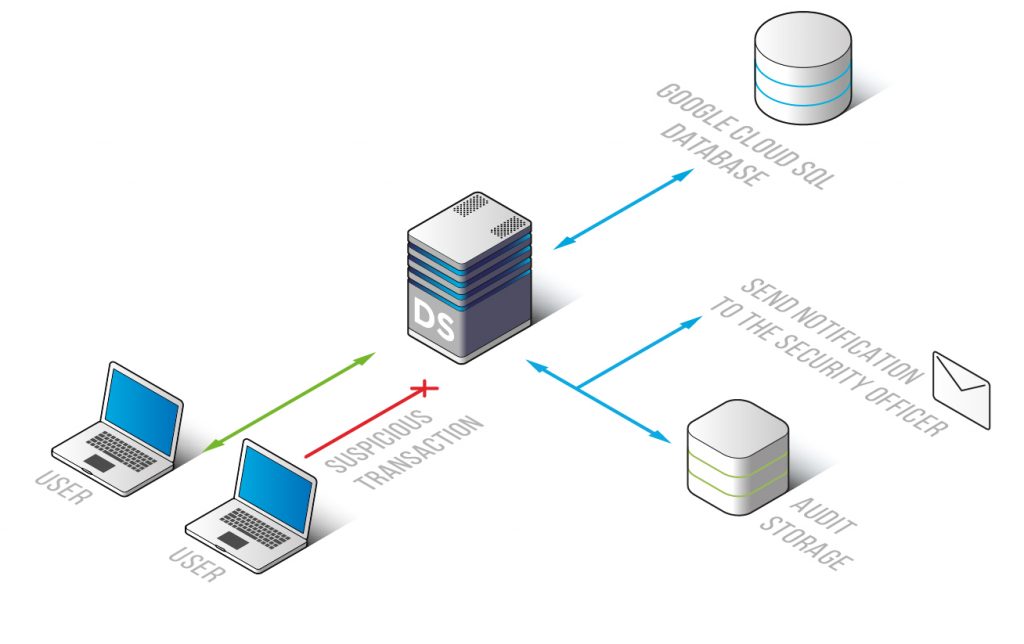
DataSunrise Data Audit is an effective and reliable tool for continuous activity monitoring and logging all the events took place in Google Cloud SQL. Audit logs contain detailed information on incoming queries and the results of their execution. Functioning as a proxy between the server and users, DataSunrise keeps you aware of what’s happening in your cloud database.
Audit is an important unit in database security system as it provides a clear picture of what’s happening in your cloud server. DataSunrise is deployed as a proxy service, thus it intercepts all queries from users and saves the detailed description of database activity. Our product will provide you with some significant benefits:
- No impact on performance characteristics;
- User-friendly interface;
- Compliance with standards of HIPAA, SOX, PCI DSS and other regulators;
- Assistance in revealing potential vulnerabilities and insider threats;
- Self-learning mode.
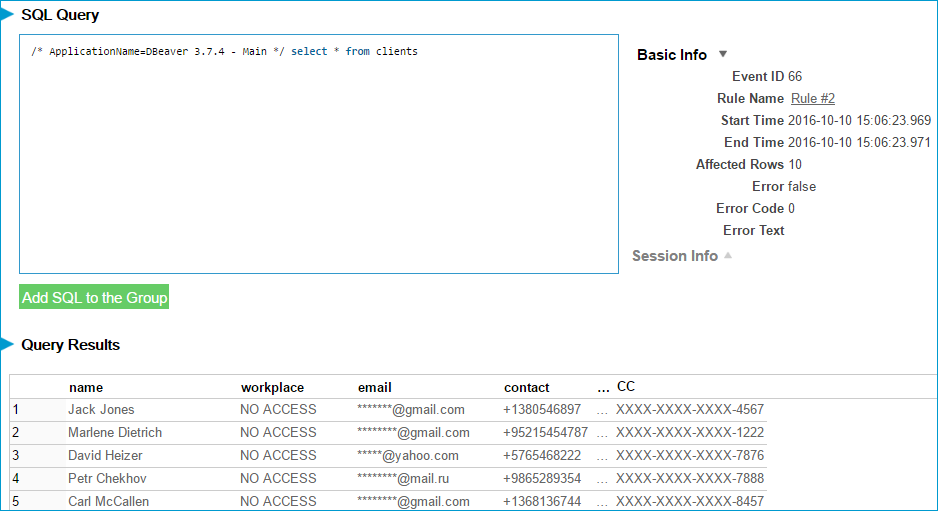
In case of a data leak audit logs will provide with all required information to investigate the incident and evaluate the cost of damage. DataSunrise collects detailed information on intercepted queries, including IP address the query came from, application name, time and number of affected rows. Clicking certain query you can view the code of any SQL query and the result of its execution. This will help you to find the culprit of a data leak.
System Events section allows seeing what configuration changes have been applied to the database: who attempted to enter the database, changes made to masking, audit or security rules, errors occurred. Regular monitoring helps to detect suspicious operations of company employees. Switch on notifications of certain security rules and be aware of any peculiar activity happening on your cloud database. More detailed information on monitoring feature is available here.
Results of the audit can be exported to SIEM-solutions that provide real-time analysis of security alerts generated by applications and network hardware. DataSunrise has a self-learning feature which simplifies working with the system by analyzing incoming queries and preparing a list of SQL queries that are typical for employees of the company.
DataSunrise Data Audit for Google Cloud SQL is a high-quality security tool that will perform continuous monitoring of all actions in your cloud server and prepare reports to comply strict standards established by government and regulators, such as SOX, PCI-DSS, HIPAA and others. Elevate your data security strategy with DataSunrise Audit. Book your online demo today and see our powerful tools in action.


