DataSunrise Audit for Amazon Aurora
Amazon Aurora data audit software by DataSunrise enables to get a full picture of database activity. Knowing who, why and when queried your database is more than just helpful, especially when working in the cloud. Moreover, continual data auditing plays an important role in database security as well. When paired with SIEM system, DataSunrise helps not only to reveal data theft that has already occurred, but to detect data breach preparations beforehand.
Common information about Amazon Aurora Data Audit
Amazon Aurora Audit by DataSunrise is a powerful database activity monitoring (DAM) solution. Here are some typical use cases for DAM technology:
- Monitoring privileged users behavior. Yes, database administrators also pose a potential threat to your data security. They can hide their malicious activity within the database but can do nothing with DAM solution.
- Detecting suspicious user activity, whether it’s just a nosy employee or a malicious attacker trying to cause harm or disruption. Knowing about suspicious activity helps to catch data breach attempts early on.
- Revealing dormant user accounts and other vulnerabilities that can be exploited by hackers.
- Revealing and investigating data leak. Sometimes you don’t even suspect that your data is stolen. DAM helps you to reveal already-occurred data breach and conduct proper investigation.
- Many regulatory compliance standards (SOX, PCI DSS, HIPAA, etc.) require organizations to employ data audit and database activity monitoring.
- Collecting statistics.
More detailed information on monitoring feature is available here.
Amazon Aurora Data Audit
DataSunrise provides ongoing tracking of database activity. It captures and documents user actions and all changes applied to database tables. DBAs can easily find out who and when accessed the database.

The firewall is deployed as a proxy positioned between clients and the database:
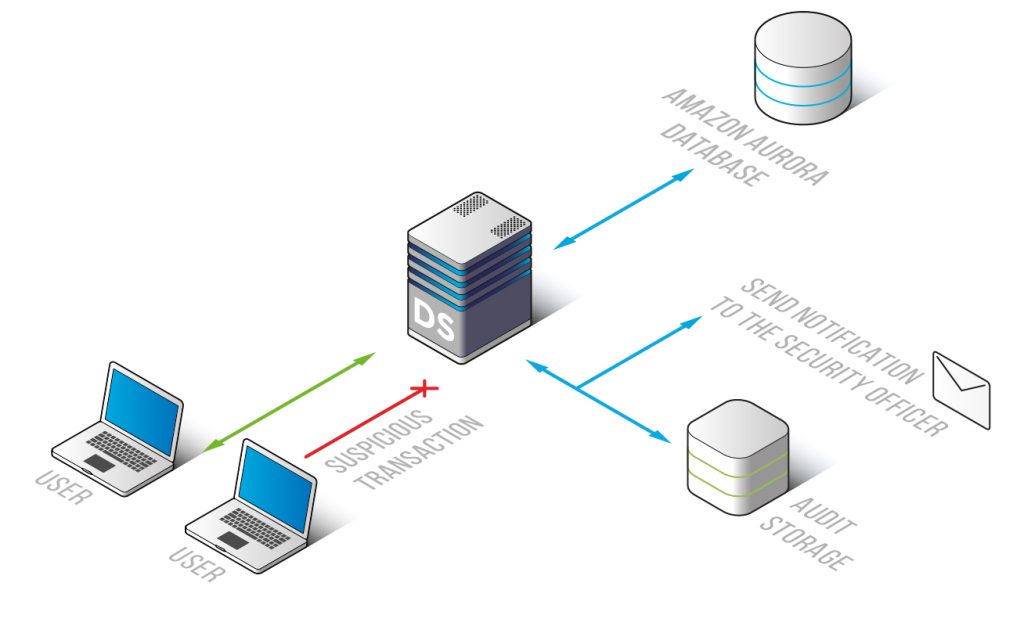
Amazon Aurora Audit results are saved into DataSunrise-integrated SQLite database or to external database (audit storage). In case of integrating DataSunrise Amazon Aurora Audit into a third-party solution, the collected data can be seamlessly exported to an external system (e.g. SIEM). When paired with SIEM system the DataSunrise Amazon Aurora Audit component enables you to get the whole picture of database user activity.
Additionally, DataSunrise features self-learning functionality, Learning mode. DataSunrise logs typical database events and creates a white list of queries considered as «safe» in given database environment.


